Phishing scams are emails or social media messages that seem to be from a legitimate company and ask for your account information to verify or settle some transaction or issue. Often, these messages will come from a company you’re about to do business with. Here we will go through some of the most common ways to recognize and avoid phishing scams for business owners.
Need to Explore Your Options?
Anti-Phishing Software & Services
Anti-phishing software and services can be a good way to help protect yourself from phishing scams. As phishing attacks become more clever, these tools continue to evolve to help potentially warn you if a phishing link is dangerous. Some anti-phishing software will allow you to report suspicious links to your email provider to help improve their database and detections over time.
Know What a Phishing Scam Looks Like
A social engineering scam is a phishing scam. This phishing scam manipulates targets into giving sensitive information through social interaction.
Many social engineering scammers will pose as family members and add people off the persons social media account that they are impersonating, then try and get the members to fall into their scam. Phishing attempts can also come in the form of emails that have malicious links or files in the.
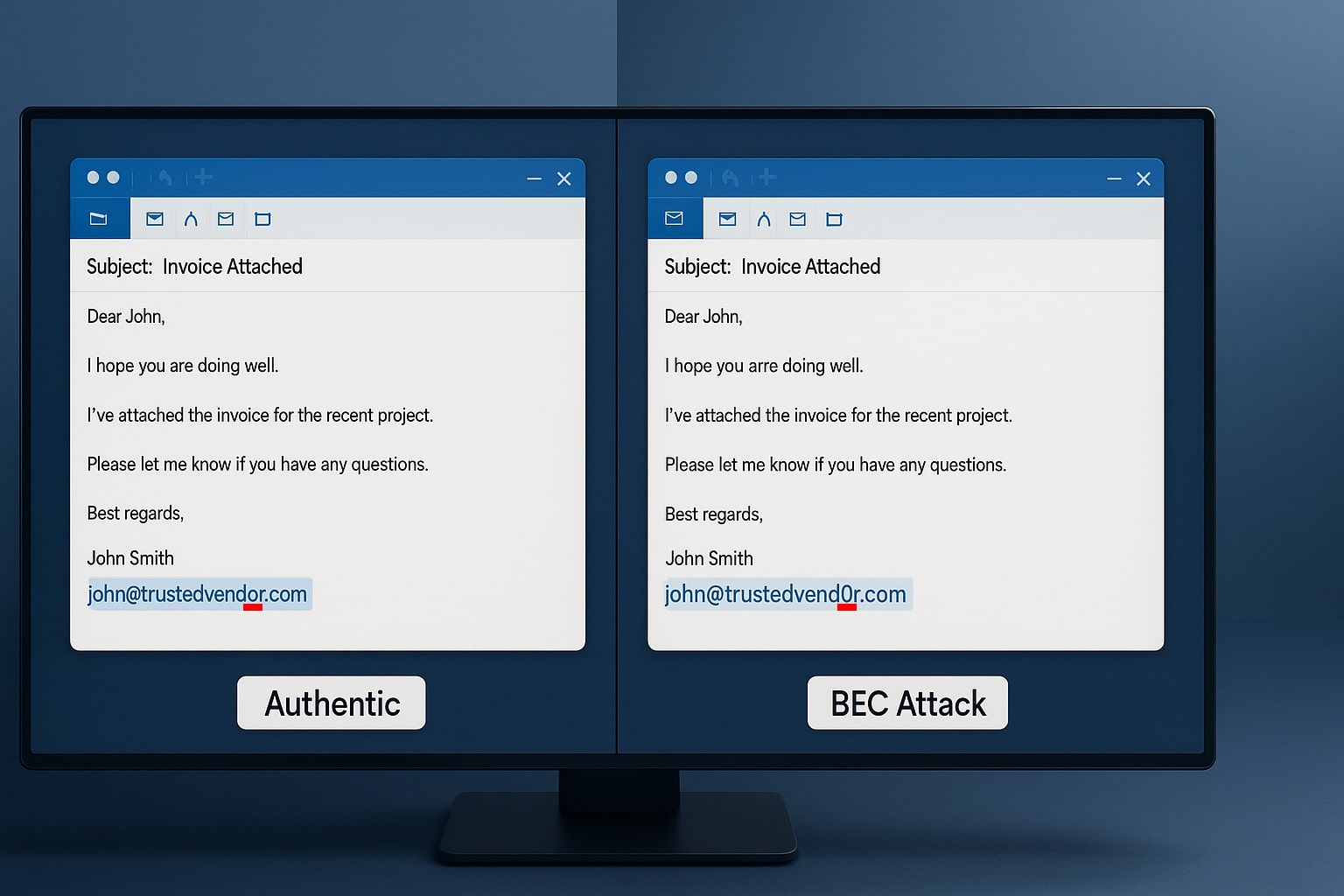
For example, a phishing email requests corporate-level personnel to click on a link to access an online credit card processor. The logo incorporated by the scammer looks remarkably like that of the financial institution they claim to be a part of. That is why it is so important for you and those apart of your organization to be able to recognize a phishing scam by looking at it at first glance. If an email feels off in any way, it is almost always off.
Have Someone not Involved Check Links to Confirm Validity
A good way for you to avoid falling for phishing scams is to have a third party make sure that it is a valid link. This includes employees, clients, or vendors. A person not involved in the transaction may catch subtle variations in the design or spelling of a website address that would go unnoticed by people who recognize the company logo and trust their intentions.
This is one of the most effective ways to spot phishing scams and avoid them at all costs. This is why many businesses turn to MSP’s and Cybersecurity Providers because they can forward malicious seeming emails to them for them to check out further without having to worry any more about it.
Need to Explore Your Options?
Use a Professional Service to Conduct Online Research
You should also use professional services to conduct online research, especially when dealing with negotiation and sales. These services will provide insight into what you should look for so that you can spot phishing scams, just like anti-phishing software, but they can also help you avoid them entirely by showing you exactly what to look for in terms of warnings.
Use a Safe Browsing Tool
When avoiding phishing scams, you should use a safe browsing tool. It will assist you in recognizing phishing scams on the web and possible exploits that could cause your computer to be vulnerable. You will also want to watch your security software for the latest updates and scans. Also, get everyone on your team to use anti-phishing software and safe browsing tools.
Using a safe browsing tool will ensure that none of them are ever victims of a phishing scam. If you have employees or contractors that do not use these tools, this can cause your entire organization to be at risk of falling for a phishing scam.
Don’t be Tempted by Pop-ups
The most common phishing scams that people fall for are pop-ups. These pop-ups often appear at the top of your internet browser and look like a bank or financial institution notice. It could have a message that says, your password needs to be changed. Sometimes the message is well written, up until you click on it. Often, these pop-ups will be fake and are part of phishing scams. You should avoid clicking on these pop-ups to prevent phishing.
Need to Explore Your Options?
Get the Boynton Beach Cybersecurity You Need
In conclusion, recognizing and avoiding phishing scams is a critical aspect of cybersecurity in Boynton Beach. With the rise of Boynton Beach Ransomware attacks, it is important to stay informed and take proactive measures to protect your personal and business information.
By being vigilant, educating yourself and your employees, and investing in reliable cybersecurity solutions, you can minimize the risk of falling victim to these malicious attacks. At Blue Light IT, we are dedicated to providing top-notch cybersecurity services to keep your data safe. Contact us today for a consultation and let us help you safeguard your digital assets.
Related Posts
The $287,000 Email Mistake
read more

Did You Know There Are Multiple Types of Phishing? (2025 Edition)
read more

