
Cybercriminals are getting smarter, and phishing attacks are evolving. What used to be simple email scams have now expanded into highly targeted, multi-channel attacks designed to steal credentials, install malware, and even take over entire business operations.
Phishing isn’t just one thing, it comes in different forms, each with its own tactics.
Here’s what you need to watch out for in 2025.
Phishing (Classic Email Scams)
Phishing is the broadest and most well-known type of cyber scam. Attackers send mass emails impersonating trusted companies, think fake alerts from your bank, Amazon, or Microsoft, designed to trick you into clicking malicious links or providing login credentials.
But phishing isn’t just a numbers game anymore. Advanced phishing tactics use AI to craft realistic, personalized emails, making them harder to detect. Even security-conscious users can be fooled by well-executed attacks.
Need to Learn More How to Keep Your Business Protected?
Vishing (Voice Phishing)
Vishing scams use phone calls to manipulate victims into giving up sensitive data. Attackers may pose as bank representatives, tech support, or even the IRS, claiming your account has been compromised. The goal? To get you to share financial details or grant access to your computer, where malware can be installed to steal your data or lock you out entirely. AI-generated voice deepfakes are becoming a major threat in 2025, allowing scammers to convincingly impersonate real people, including executives and coworkers.
Smishing (SMS Phishing)
Smishing attacks work like vishing but arrive via text messages instead of phone calls. You might get a message claiming to be from your bank, a delivery service, or even your employer, urging you to click a link or call a number. Once you engage, attackers may trick you into entering your credentials or downloading malware. With the rise of mobile payment scams, attackers now often use smishing to intercept transactions and gain access to financial apps.
Spear Phishing (Targeted Attacks)
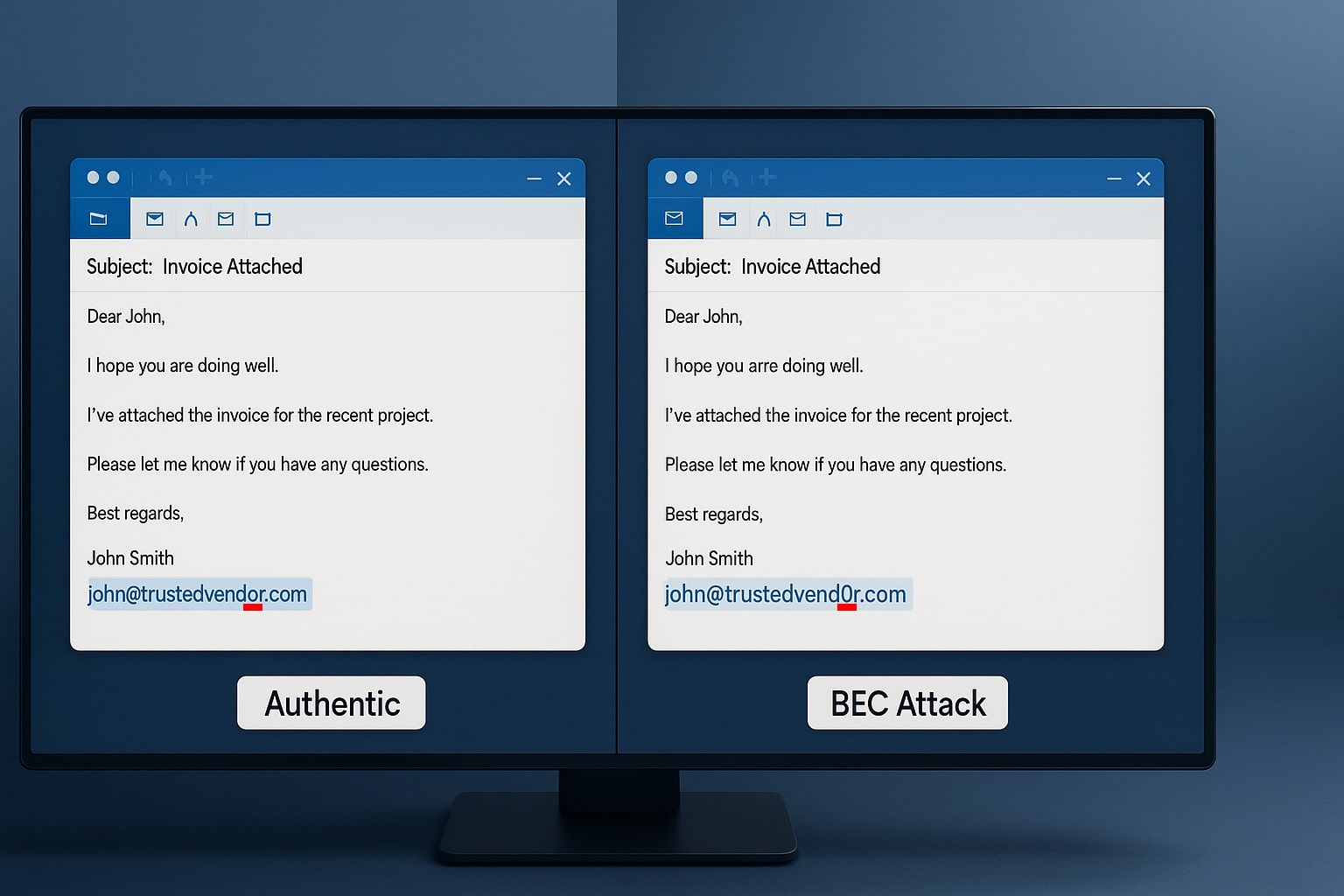
Spear phishing is highly targeted. Instead of blasting emails to random users, attackers focus on specific individuals, like employees in HR, finance, or IT, who have access to sensitive company data. These emails often appear to come from internal sources, such as a manager or CEO, making them harder to detect. AI-driven social engineering has made spear phishing even more dangerous, allowing attackers to generate highly personalized messages that mimic real conversations.
Need to Learn More How to Keep Your Business Protected?
Whaling (CEO and Executive-Level Attacks)
Whaling is a more sophisticated form of spear phishing that goes after top executives, board members, and high-ranking employees. These scams often involve urgent emails about lawsuits, financial transactions, or confidential business deals. In some cases, attackers even compromise real email accounts, making it nearly impossible to spot the fraud. A well-executed whaling attack can lead to massive financial losses, data breaches, and even reputational damage.
How to Protect Your Business in 2025
PPhishing attacks are getting trickier, and it only takes one mistake for a scammer to get into your systems. With the right training, your team can spot these scams before they turn into a costly problem. At Blue Light IT, we make cybersecurity simple. We’ll show you and your employees how to recognize phishing scams, avoid common traps, and keep your business safe, without the confusing tech talk.
Hackers aren’t slowing down, but you don’t have to make their job easy. Let’s make sure your business isn’t an easy target. Contact us today!
Related Posts
The $287,000 Email Mistake
read more

Recognize and Avoid Phishing Scams
read more

