
BLUE LIGHT IT BLOG Technology updates and cyber news • Page 1
BLUE LIGHT IT BLOG
Technology updates and cyber news


Three Years on CRN’s Security 100: What It Actually Means for Your Business
read more

Why Choose Us as Your Managed Security Service Provider in Boca Raton
read more

Why Smart Businesses Never Risk Their Data: The 2025 Guide to Bulletproof Data Backup
read more
Law Firms Beware: The Silent Ransom Group is Calling
read more
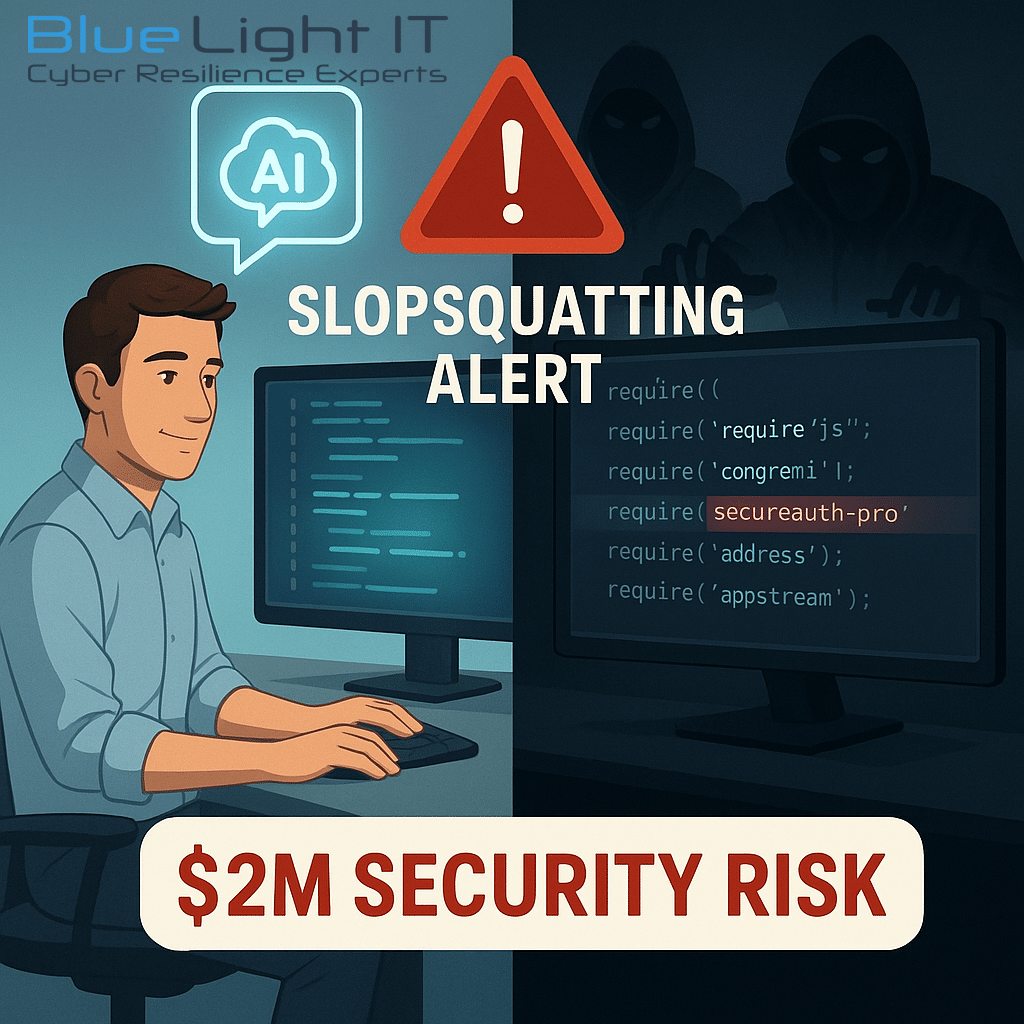
Slopsquatting: The AI Security Threat Every Development Team Must Address
read more
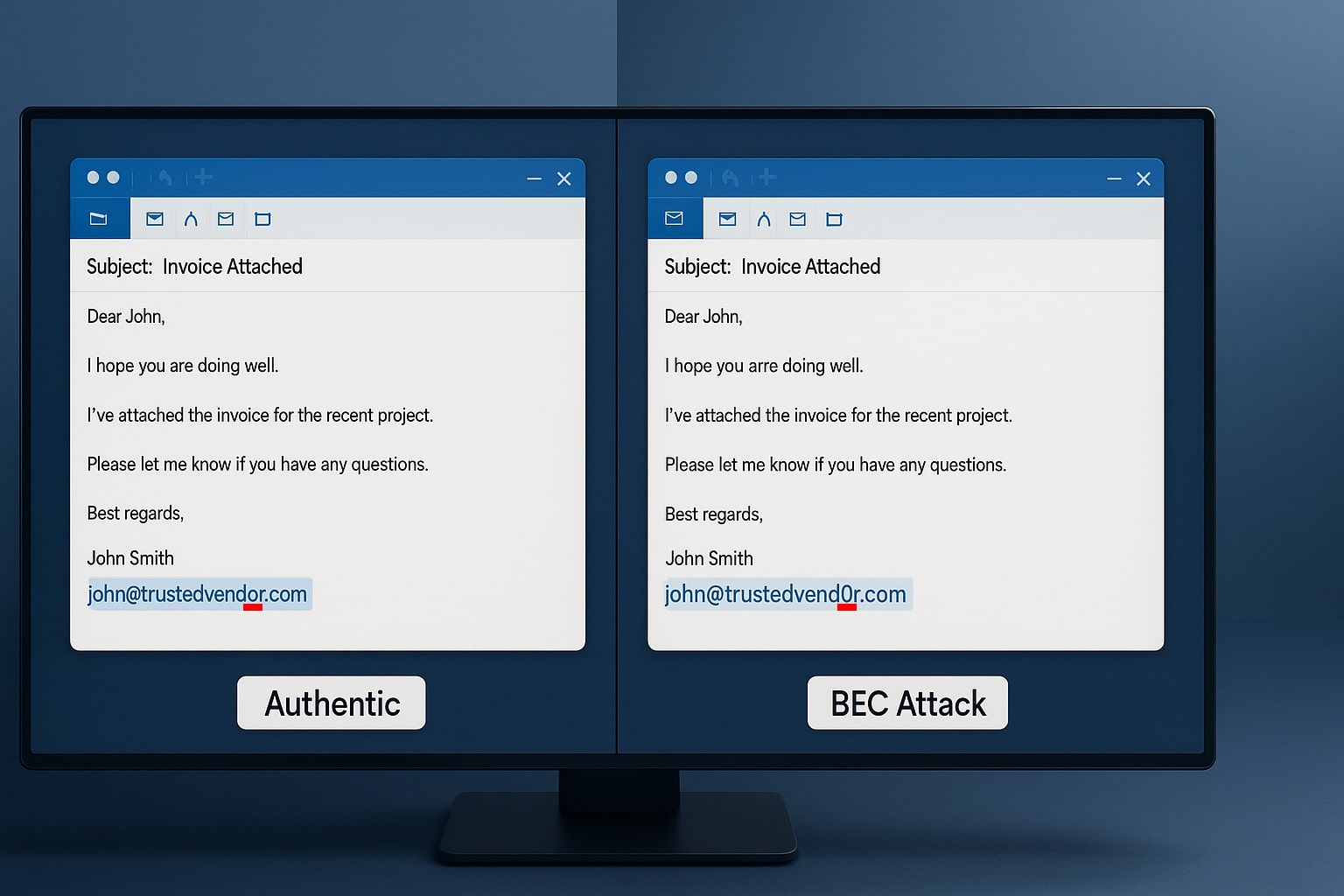
The $287,000 Email Mistake
read more

Did You Know There Are Multiple Types of Phishing? (2025 Edition)
read more
The Cybersecurity & IT Tips and News You Need - Page: 1
Wait...
Don’t leave without your free ebook.

5 Golden Rules to Increasing Your Cyber Resilience
Enter your email to receive your free ebook.
We respect your privacy. Unsubscribe at any time.
Check your inbox
Thank you for submitting your information. Check your email for your personal copy of the
5 Golden Rules to Increasing Your Cyber Resilience
Contact Us
Enter your details below and we will contact you within 1 business day.
"*" indicates required fields

